After the latest Windows Updates (June 2022) I could not logon to Office 365 using a federated domain (Microsoft Teams in particular, the mailboxes are in Exchange 2019 for this domain), regular domains did not experience any issues.
Trying the regular ADFS URLs did not help, the site was not available:
- https://federation.contoso.com/adfs/fs/federationserverservice.asmx
- https://federation.contoso.com/federationmetadata/2007-06/federationmetadata.xml
- https://federation.contoso.com/adfs/ls/idpinitiatedsignon.htm
When checking the WAP server I noticed the WAP service was not running and was not willing to start. At the same time, EventID 224 was logged in the eventlog with the “The federation server proxy configuration could not be updated with the latest configuration on the federation service” error messages as shown in the following screenshot:
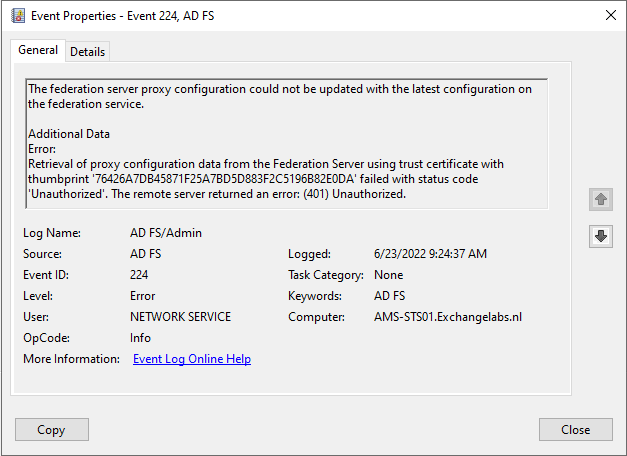
Especially the additional data reveals a lot:
Retrieval of proxy configuration data from the Federation Server using trust certificate with thumbprint ‘76426A7DB45871F25A7BD5D883F2C5196B82E0DA’ failed with status code ‘Unauthorized’. The remote server returned an error: (401) Unauthorized.
At the same time, Event ID 276 is logged on the internal ADFS Server:
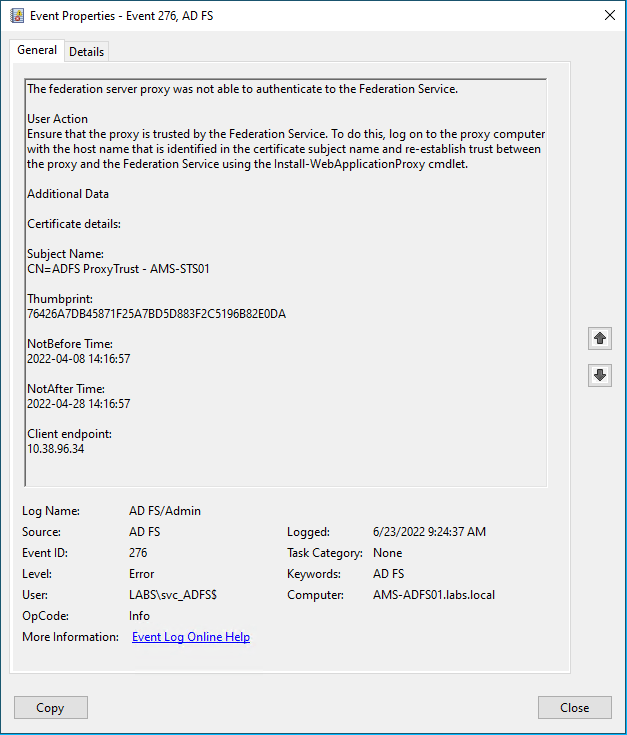
Obviously, the trust between the proxy server and the ADFS server is broken (it has been some time when I look at the timestamps, this happens in a test environment 😊) so the trust relationship needs to be re-established.
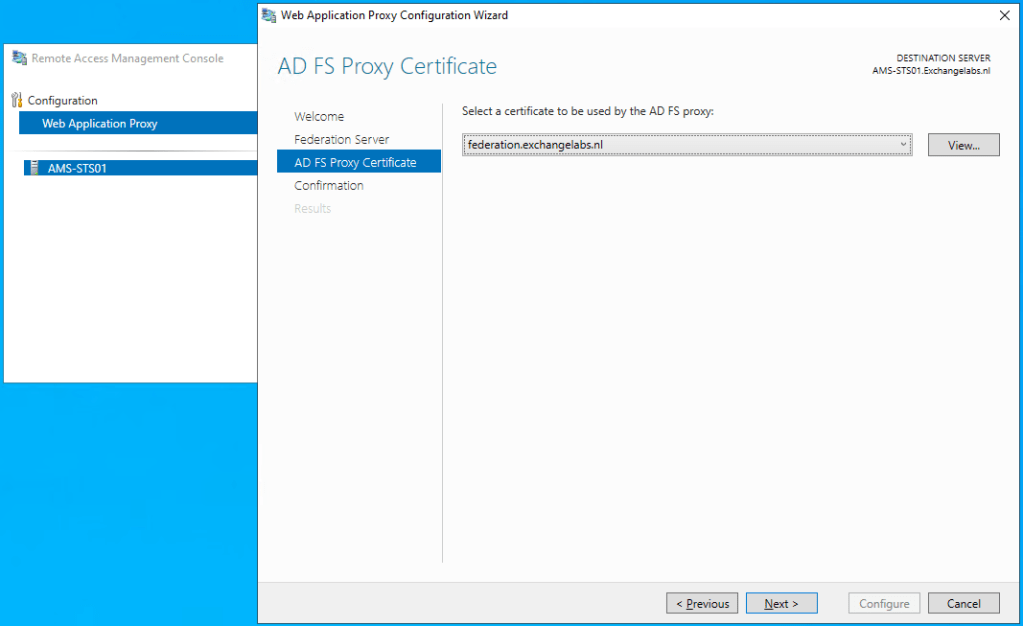
This can be done using the wizard in the Remote Access Management Console:

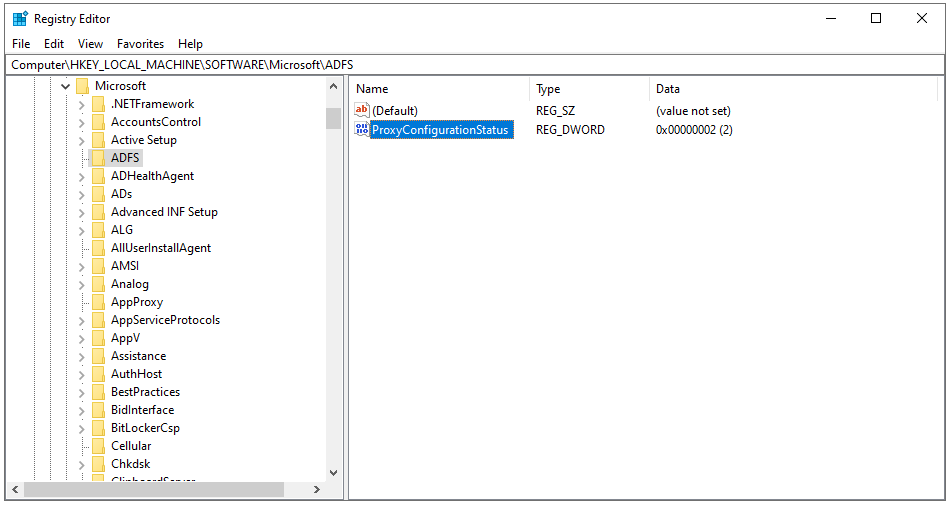
If you get a warning message like “Web Application Proxy could not connect to the AD FS configuration storage and could not load the configuration” you must change the ProxyConfigurationStatus in the registry (HKLM\Software\Microsoft\ADFS) from “2” to “1” as shown in the following screenshot.
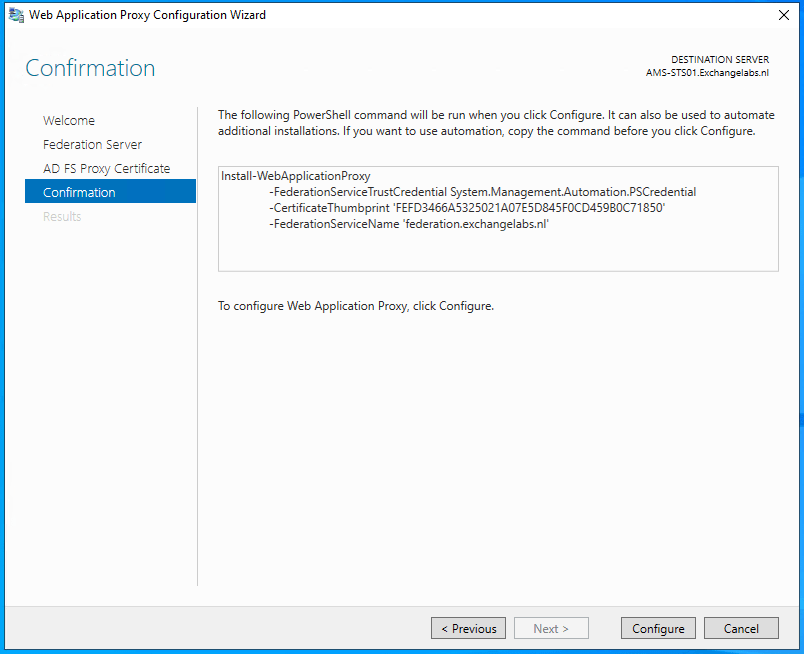
Follow the wizard, select the appropriate certificate, check the changes and click the Configure button as shown in the following two screenshots:
When you check the eventlog, you’ll see Event ID 252 with the configuration changes:

And you can see that the ADFS Proxy server can authenticate successfully:

The server is now fully functional again.