When you’ve implemented Self Service Password Reset and a cloud user (i.e. an account that only lives in the Microsoft cloud, not an on-premises Active Directory account) wants to change his password, there’s a chance the user will see the following error message:
“Choose a password that’s harder for people to guess”
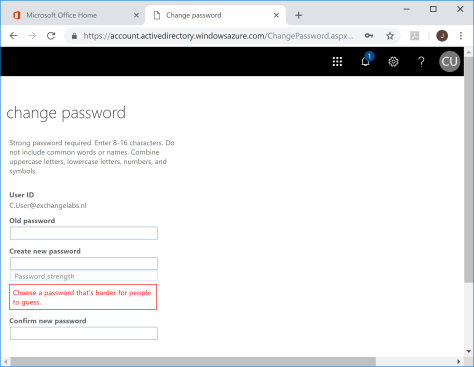
The odd thing is, when the user changes his password in the SSPR it even says the user is using a strong password as shown in the following screenshot:
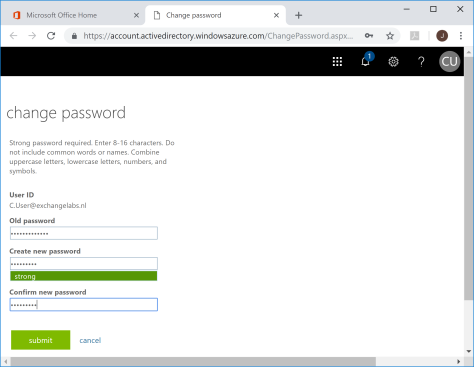
Note. I tried this with several combinations, like Pass1word, P@ssW0rd and Spring2018.
A similar error message can be “Unfortunately, your password contains a word, phrase or pattern that makes it easily guessable. Please try again with a different password.” as shown in the following screenshot:
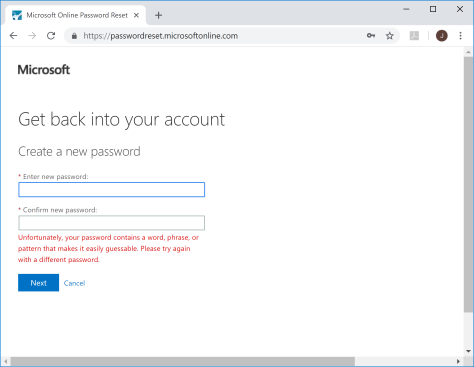
The ‘problem’ here is that the user is hitting the ‘banned password list’ in Azure Active Directory. This banned password list is a list of over 1,000 passwords that can easily be guessed, and as such vulnerable for password spray attacks. These passwords are simple words like spring, summer, autumn, winter, football, company name, qwerty, 123456, welcome, zaq1zaq1 etc etc etc. There’s a list of most common passwords on WikiPedia. Of course there are several variations of passwords, password, Pass1word, Pass!word, Passw0rd, you name it, but Microsoft is using normalization techniques to filter out all replaced characters and thus block these passwords.
Banned passwords are part of the Azure AD Password Protection feature, a feature that’s still in preview at the time of writing (October 2018). When you logon to the Azure Portal (https://portal.azure.com) and navigate to Azure Active Directory | Authentication Methods (in the security section) you’ll see the Azure AD Password Protection feature:

The banned password list is enforced by default, there’s no way to disable it. If you have an Azure AD Premium license, you can also use a custom banned password list and maintain you own list of words or phrases that you don’t want to be used as a password.
Summary
If your users run into the Choose a password that’s harder for people to guess error message when changing their password in Azure AD or Office 365, they are hitting the banned password list as part of the Azure AD Password protect feature. A feature that’s enforced by default, and implemented by Microsoft as a means to improve security.
This feature is available for cloud users only by default, but if you have implemented self service password reset (SSPR) with password writeback it also works. The nice thing is, it can also be extended to on-premises Active Directory for password changes on-premises. Nice topic for an upcoming blog.
You must be logged in to post a comment.