| Update. Microsoft has changed their plans due to the Covid-19 crisis going on at the moment. Support for Basic Authentication in Exchange Online has been postponed to the second half of 2021 according to their blogpost on Basic Authentication and Exchange Online – April 2020 Update.
There are a few things to be aware of. For new tenants, Basic Authentication is already turned off, for older tenants it is still turned on. However, if Basic Authentication has not been used in a tenant it will be turned off as well. This will start upcoming October. |
Microsoft will stop support for basic authentication in October 2020 as outlined in the following blogpost: Basic Auth and Exchange Online – February 2020 Update. By doing this Microsoft increases security in (especially) Exchange Online, since basic authentication is a perfect attack vector for malicious users.
But what does it mean? Clients that use Exchange Web Services (EWS), ActiveSync, PowerShell, POP3 and IMAP4 and authenticate using basic authentication will stop working. Which clients are we talking about? Basic authentication only stops for Exchange Online and not for Exchange on-premises, but what happens when you are using a hybrid scenario? Of using Outlook for iOS in combination with an on-premises mailbox.
In this blogpost I’ll try to dive a bit deeper into authentication and explain what is going to happen.
Basic Authentication
Basic Authentication is one of the oldest ways of authenticating in any web application. You access an application, a dialog box is presented, you enter your credentials and the credentials are sent (in clear text) across the wire. To improve security typically an SSL connection is used, so the connection between the client and the server is encrypted.
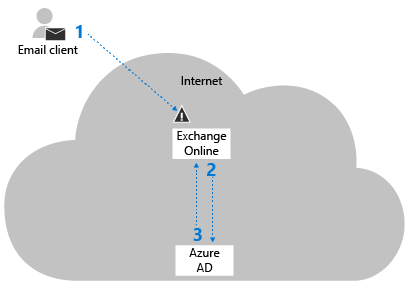
For Exchange Online this means the (Outlook) client sends it credentials in clear text to Exchange Online, and Exchange Online authenticates against Azure AD as shown in the following screenshot:
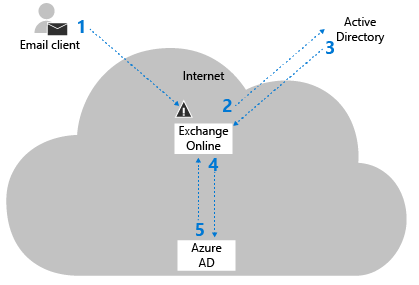
When using ADFS, basic authentication is not very different. The client authenticates and sends the credentials in clear text to Exchange Online, and Exchange Online takes care of the remaining communication using ADFS and the on-premises Domain Controllers (step 2 and 3 in the following screenshot):
Important to note is that the client here still use basic authentication.
So what clients are using basic authentication? Outlook 2010 is the most common, but also lots of ActiveSync clients, POP3 and IMAP4 clients, PowerShell and Exchange Web Services (scripts and tools!) are still using basic authentication.
I leave it up to your imagination what will happen when Microsoft stops support for basic authentication (step 1 in the screenshots above) this October!
Modern Authentication
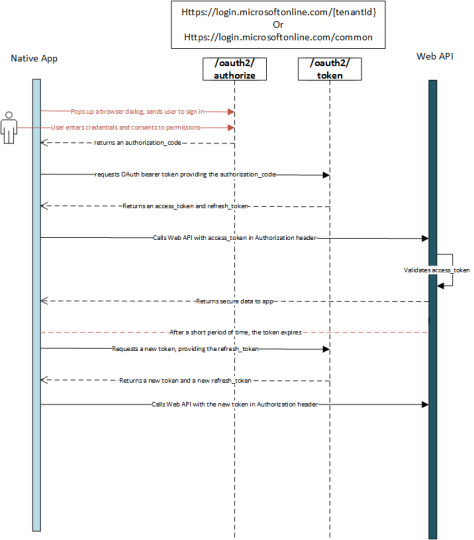
Modern authentication is a token-based authentication mechanism and as such it has similarities with federation services. On IT Dev Connections 2017 in San Francisco I did a presentation on this subject. The following screenshot is an animated slide from the presentation showing the authentication flow between a client, Exchange Online, Azure AD and the on-premises Domain Controller:
Modern Authentication is based on the OAuth2 framework. When using OAuth2, you grant permissions to an application (‘consent’) to contact the server on your behalf. The client contacts the server the first time and you enter your credentials in a web frame, this is a server-based web frame and when the credentials are entered two tokens are generated:
- Access token, which is used to access various services.
- Refresh token, which is used to renew the access token when it is about to expire.
This is shown in the following image:
Source: Authorize access to Azure Active Directory web applications using the OAuth 2.0 code grant flow.
The access token is constantly renewed (and thus no need to re-authenticate manually) until it cannot be renewed, for example when the password expires, the account is blocked (the access token is revoked) or when a Conditional Access policy can no longer be applied. In all these scenarios access to the service is denied.
Outlook 2013 and higher support Modern Authentication. In Outlook 2013 you had to set some registry keys, but in Outlook 2016 and higher it is enabled by default.
The way to identify if you are using modern authentication is the HTML based login screen which look like this:
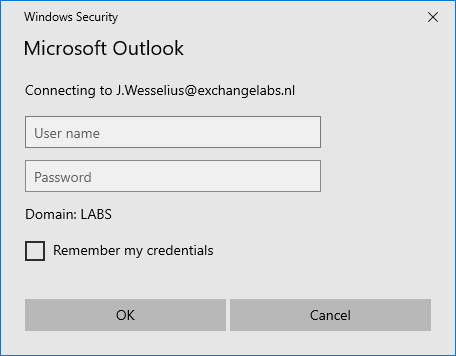
While the basic authentication (in Exchange 2016, but similar in Outlook 2010) looks like:
Another way to identify Modern Authentication is to use the connection status in Outlook:
When you see ‘Bearer’ (coming from OAuth bearer token) Outlook is using Modern Authentication, if you see ‘Clear’ then basic authentication is used by Outlook.
Summary
In this first part I have tried to explain the difference between basic authentication and modern authentication, how modern authentication works and how to identify which authentication method your Outlook client is using.
In my next blog (Part II) I will explain more about how to monitor basic authentication and how to start testing what happens when disabling basic authentication.



2 thoughts on “Basic Authentication in Office 365 Part I”