In my previous blog External Senders with matching display names I explained a Transport Rule that checked for matching display names in order to prevent phishing and possible CFO Fraud.
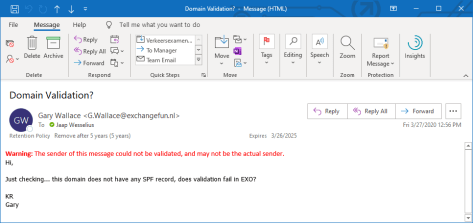
Another interesting solution with Transport Rules is displaying a warning message when the sender’s domain could not be validated. For example, when a message from a sender who’s SPF record is missing or not valid, it would show something like “The sender of this message could not be validated and may not be the actual sender” as shown in the following screenshot.
In this example the SPF record of the exchangefun.nl domain was missing, hence the validation error.
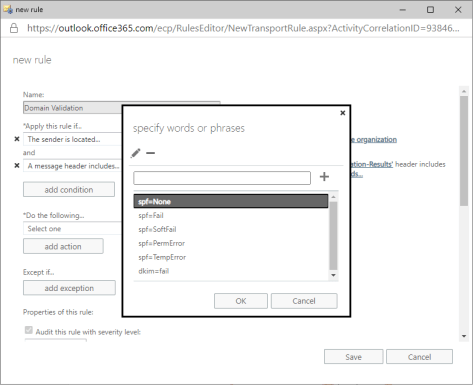
- The Transport Rule to achieve this is built on two conditions:
- The sender is located outside the organization.
The Authentication-Results headers contains one or more of the following entries:
- dkim=fail
- spf=TempError
- spf=PermError
- spf=SoftFail
- spf=Fail
- spf=None
For the email mentioned below, the Authentication-Results header shows the following:
Authentication-Results: spf=none (sender IP is 176.62.196.243)
smtp.mailfrom=exchangefun.nl; wesselius.info; dkim=pass (signature was verified) header.d=Exchangefun.nl;wesselius.info; dmarc=permerror action=none header.from=exchangefun.nl;compauth=pass reason=105
Obviously, it fails on the spf=none entry.
To create a Transport Rule to do this, open the Exchange Online Admin Center and navigate to Rules under Mail Flow and click Add New Rule (the + icon). Use the More Options to add additional conditions to the Transport Rule.
The first condition is The sender is located and select outside the organization. The second condition is A message header includes and enter Authentication-Results for the name of the header and the DKIM and SPF entries mentioned earlier in the text of the message header. It should show something like this:
Click on Add Action and select Prepend a disclaimer. Enter a warning message like:
Warning: The sender of this message could not be validated and may not be the actual sender.
The text can be plain text or HTML formatted as shown in the following screenshot:
When you click Save the Transport Rule is saved in Exchange Online. It could take up to an hour to become effective. And when you receive a message where the domain validation failed a disclaimer is prepended to the email message:
Now you can look in the message header itself to figure out why validation failed. Hopefully this will give a heads-up to users there’s something wrong with the message (but it still can be legitimate message of course).
A special and warm thanks to my fellow MVP Michel de Rooij for his inspiration to write this blog 😉




You must be logged in to post a comment.