When installing an Exchange 2013 Edge Transport server a self-signed certificate is created and configure for use with the SMTP Transport server. The self-signed certificate has the NetBIOS hostname as the Common Name and the FQDN in the Subject Alternate Names field.
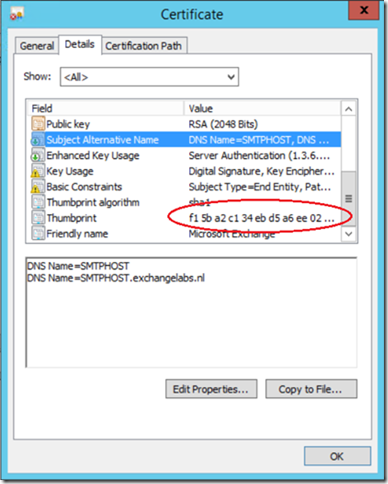
You can view this self-signed certificate using the Certificate MMC snap-in:
Continue reading Exchange 2013 Edge Transport Server and SSL Certificates