Since a couple of days my OWA and ECP are not working anymore. This happens on both Exchange 2019 CU11 and Exchange 2016 CU22, in two AD sites both with external access. I didn’t notice before since Outlook Mobile and Outlook on the desktop continue to work. After logging in, the Something went wrong message appears, in the navigation bar you can see it is an Error 500 message.

I think (but I’m not sure) that this started after applying the latest November 2021 Security Updates and this is usually caused by starting the Security Update without elevated privileges. There’s an Microsoft article about this: OWA or ECP stops working after you install a security update – Exchange | Microsoft Docs.
I am pretty sure that I installed the Security Update with elevated privileges, but also after reinstalling the Security Update (with elevated privileges!) the error continues. The Microsoft article also mentions settings in IIS Manager (Application settings > BinsearchFolder), but that was not the issue (settings were ok).
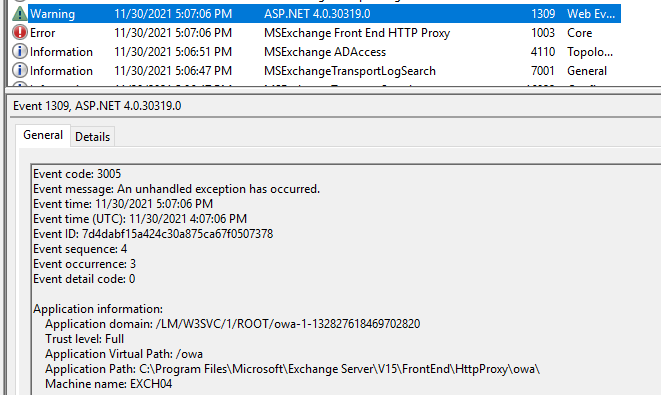
When authentication fails, two entries are written in the Application Eventlog, EventID 1003 (MSExchange Front End HTTP Proxy) and EventID 1309 (ASP.NET 4.0.30319.0). The latter clearly shows it has something to do with certificates:

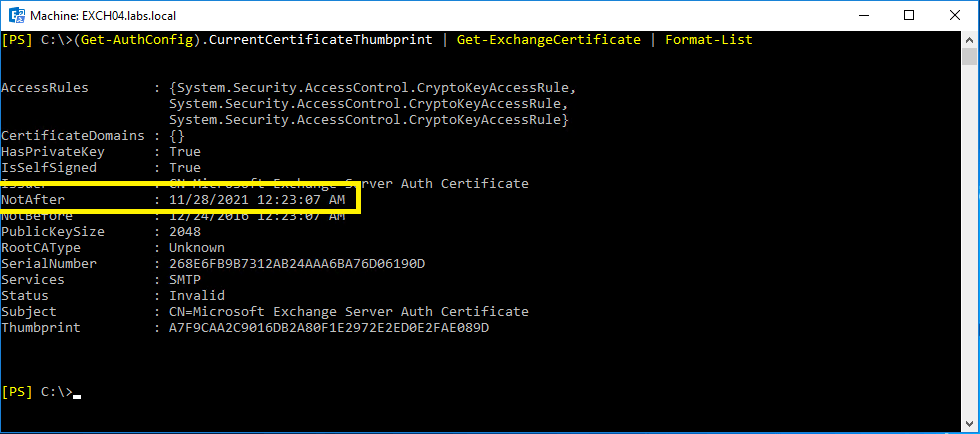
It turned out that the Exchange Server Auth Certificate was expired, just a few days ago. You can see this when running the following command:
[PS] C:\>(Get-AuthConfig).CurrentCertificateThumbprint | Get-ExchangeCertificate | Format-List
AccessRules : {System.Security.AccessControl.CryptoKeyAccessRule,
System.Security.AccessControl.CryptoKeyAccessRule,
System.Security.AccessControl.CryptoKeyAccessRule}
CertificateDomains : {}
HasPrivateKey : True
IsSelfSigned : True
Issuer : CN=Microsoft Exchange Server Auth Certificate
NotAfter : 11/28/2021 12:23:07 AM
NotBefore : 12/24/2016 12:23:07 AM
PublicKeySize : 2048
RootCAType : Unknown
SerialNumber : 268E6FB9B7312AB24AAA6BA76D06190D
Services : SMTP
Status : Invalid
Subject : CN=Microsoft Exchange Server Auth Certificate
Thumbprint : A7F9CAA2C9016DB2A80F1E2972E2ED0E2FAE089D
As shown in the following screenshot:
Use the New-ExchangeCertificate command to create a new self-signed certificate for authentication purposes:
[PS] C:\>New-ExchangeCertificate -KeySize 2048 -PrivateKeyExportable $true -SubjectName "cn=Microsoft Exchange Server Auth Certificate" -FriendlyName "Microsoft Exchange Server Auth Certificate" -DomainName @()
Confirm
Overwrite the existing default SMTP certificate?
Current certificate: 'D7081FC32B9BFBEF0C0581584976F690D5F86E74' (expires 11/30/2026 5:21:19 PM)
Replace it with certificate: '309263C8C5B2DA9612E8A6FA9FFFCDEBAC93335D' (expires 11/30/2026 9:00:56 PM)
[Y] Yes [A] Yes to All [N] No [L] No to All [?] Help (default is "Y"): n
Thumbprint Services Subject
---------- -------- -------
309263C8C5B2DA9612E8A6FA9FFFCDEBAC93335D ....S.. CN=Microsoft Exchange Server Auth Certificate
As shown in the following screenshot:

When the certificate is created, the AuthConfig needs to be configured, it needs to be published and the old (and expired) certificated needs to be removed. Use the Set-AuthConfig command to achieve this:
[PS] C:\>Set-AuthConfig -NewCertificateThumbprint 309263C8C5B2DA9612E8A6FA9FFFCDEBAC93335D -NewCertificateEffectiveDate (Get-Date)
Confirm
The new certificate effective date is not at least "48" hours in the future and may not be deployed on all necessary
servers. Do you wish to continue?
[Y] Yes [A] Yes to All [N] No [L] No to All [?] Help (default is "Y"): y
[PS] C:\>Set-AuthConfig -PublishCertificate
[PS] C:\>Set-AuthConfig -ClearPreviousCertificateAs shown in the following screenshot:

Restart the Microsoft Exchange Service Host service and perform an IISRESET. If you cannot run IISRESET you can also recycle both the OWA and ECP App pool:
[PS] C:\> Restart-WebAppPool MSExchangeOWAAppPool
[PS] C:\> Restart-WebAppPool MSExchangeECPAppPool
The certificate is stored in Active Directory in CN=Auth Configuration, CN=, CN=Microsoft Exchange, CN=Services,DC=, DC= as shown in the following screenshot:

Since it is published in Active Directory, the new certificate will be automatically available for all Exchange servers in your organization. It can take up to an hour before it is fully published and available, so don’t worry when it doesn’t work immediately.
Please be aware that you do this only on one Exchange server. If you (accidentally) do this on multiple Exchange servers, you will see multiple Auth Certificates appear on your Exchange server. But only the last one created will be active though.
Only two steps remain:
- Remove the old Auth Certificate on all Exchange servers. You can do this using EAC or using PowerShell (Remove-ExchangeCertficate -Server -Thumbprint <old certificate).
- Run the Hybrid Configuration Wizard again to update the new certificate in Azure Active Directory.


You must be logged in to post a comment.