On September 28, 2021 Microsoft released their quarterly updates for Exchange server, Exchange 2019 CU11 and Exchange 2016 CU22. Despite earlier communications a new CU for Exchange 2016 is released as well.
Besides normal fixes, a new feature is introduced in these CUs as well, the Exchange Emergency Mitigation Server or EEMS. EEMS is a new service that can mitigate new security breaches when they arise. EEMS connects to a Microsoft endpoint (https://officeclient.microsoft.com/getexchangemitigations) and when needed, downloads and installs available mitigations. It performs a check once an hour. If you don’t feel comfortable with this, it is possible to disable this on an organization level 😉
Also new in Exchange 2019 CU11 and Exchange 2016 CU22 is telemetry regarding the mitigation service. When configured, it will automatically upload mitigation related service to Microsoft. Again, this can be disabled as well using the license agreement (enabled by default).
When installing this update you will see change in the License Agreement:

The default is I accept the license agreement and will share diagnostics data with Microsoft (recommended), but you can select other as well of course.
When using the unattended install, a new switch is used for accepting the License Agreement.
- /IAcceptExchangeServerLicenseTerms_DiagnosticDataON – when you allow to upload diagnostics data to Microsoft
- /IAcceptExchangeServerLicenseTerms_DiagnosticDataOFF – when you do not allow to update diagnostics data to Microsoft.
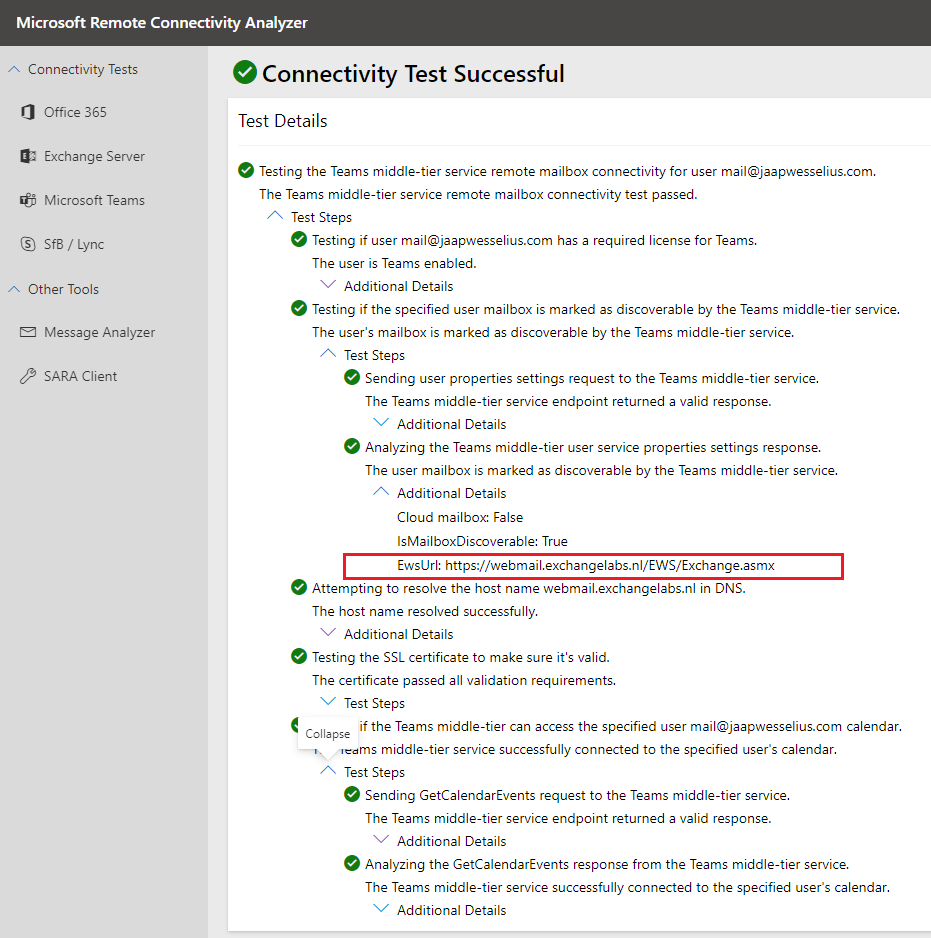
There are also two new prerequisites when installing Exchange 2019 CU11 or Exchange 2016 CU22. Prerequisite software contains now the ‘IIS URL Rewrite Module’ which needs to be installed. The second one is connectivity to the internet for accessing the mitigation service endpoint.
The setup application will check for these prerequisites and will generate an error when they are not met:

Note. The internet connectivity is not shown in this screenshot.
The ‘IIS URL Rewrite Module’ can be downloaded from https://download.microsoft.com/download/1/2/8/128E2E22-C1B9-44A4-BE2A-5859ED1D4592/rewrite_amd64_en-US.msi
Using PowerShell you can download the module, store it in the C:\Install directory and install it unattended using the following commands:
Start-BitsTransfer -Source "https://download.microsoft.com/download/1/2/8/128E2E22-C1B9-44A4-BE2A-5859ED1D4592/rewrite_amd64_en-US.msi" -Destination C:\Install
Start-Process -FilePath "C:\Install\ rewrite_amd64_en-US.msi " -ArgumentList "/q" -WaitUpdating the Exchange server to this latest CU is not different compared to earlier versions (except for the license agreement switch):
Setup.exe /PrepareSchema /IAcceptExchangeServerLicenseTerms_DiagnosticDataON
Setup.exe /PrepareAD /IAcceptExchangeServerLicenseTerms_DiagnosticDataON
Setup.exe /PrepareDomain /IAcceptExchangeServerLicenseTerms_DiagnosticDataON
Setup.EXE /Mode:Upgrade /IAcceptExchangeServerLicenseTerms_DiagnosticDataONNote. There are no schema changes when upgrading from Exchange 2019 CU10 or Exchange 2016 CU21, but there are changes when upgrading from previous releases.
After installing the updates, you will see the new services when opening the services MMC snap-in:

Or when using the Get-Service MSExchange* PowerShell command:

To check the status in the Exchange organization, you can use the Get-OrganizationConfig | Select mitigations command:

To disable the mitigation service, execute the following command:
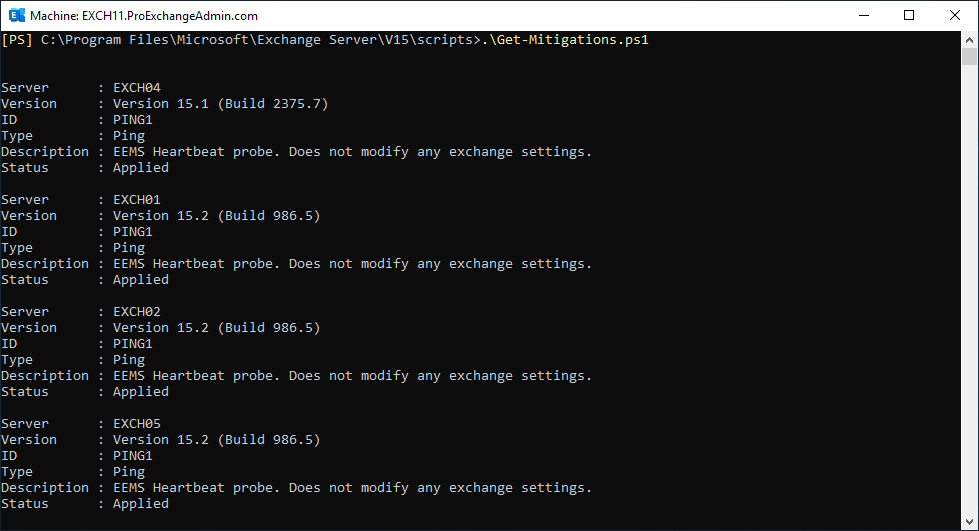
Set-OrganizationConfig -MitigationsEnabled:$FalseBy default, only one mitigation is installed, this is the EEMS heartbeat probe. You can check the installed mitigations by navigating to the Exchange scripts directory and execute the Get-Mitigations.ps1 script:
As with any Cumulative Update, please test this CU in your lab to see if all works well for your environment. Also have a look at the telemetry configuration (is that allowed in your organization?) and at the automatic configuration changes made by the EEMS (I can hear CISO starting to complain).
More information and downloads regarding the Cumulative Updates can be found here:
- Cumulative Update 11 for Exchange Server 2019 (KB5005334) (microsoft.com)
- Download Cumulative Update 11 for Exchange Server 2019 (KB5005334) from Official Microsoft Download Center
- Cumulative Update 22 for Exchange Server 2016 (KB5005333) (microsoft.com)
- Download Cumulative Update 22 for Exchange Server 2016 (KB5005333) from Official Microsoft Download Center
- Download Exchange Server 2016 CU22 UM Language Packs from Official Microsoft Download Center







You must be logged in to post a comment.